Businesses seeking to beef up their IT security have many options today. The security as a service (SECaaS) model delivers an effective and affordable means to address this important need.
And beefing up IT security is more important than ever. The advent of the coronavirus pandemic led to increased use of the internet across all areas of society from online shopping to remote work and school. This increase created new opportunities for cybercriminals.
According to the FBI, the number of reported cyber threats more than tripled after the pandemic to over 3,000 per day. This makes internet security a high priority for every organization.
But implementing robust IT security is a challenge, particularly for small businesses with limited in-house IT capabilities. SECaaS provides the answer to this problem.
Overview: What is security as a service (SECaaS)?
Security as a service involves hiring outside companies to manage the security technologies for your organization. You pay a monthly subscription fee for a set of security-related IT services.
SECaaS offerings are usually delivered through a cloud-based software platform. This security software as a service approach affords businesses lots of flexibility. You combine the cloud security components you need into a holistic solution tailored to your business.
For example, you can have a team of security experts involved in threat hunting -- proactive actions to catch cyberattacks lurking in your IT network. Other SECaaS features focus on automating routine security functions, including identity as a service (IDaaS).

Cybercrime incidents keep climbing as the FBI’s IC3 data illustrates. Image source: Author
4 benefits of SECaaS
An advantage of cloud security as a service is that it grants you the ability to craft a tailored solution to fit your specific needs. But it also supplies several other benefits.
1. Expertise
Thorough and correctly implemented IT security is necessary to effectively stop cyber threats. Rather than trying to acquire this expertise yourself, you can leverage the knowledge and experience of a SECaaS provider.
The SECaaS vendor can offer recommendations, point out opportunities for improvement in your current security setup, and provide insight into what to do when an attack occurs. And it’s responsible for providing always-on security 24 hours a day, 365 days a year.
SECaaS vendors are also plugged into threat intelligence. They’re able to leverage this information to continually improve tools and services. This constant evolution is necessary to keep pace with cybercriminals who continually seek ways to circumvent your defenses.
A vendor’s SECaaS software can provide automated recommendations to plug security holes. It monitors your IT systems continuously, seeking out not just signs of a threat but also vulnerabilities, and alerts you to these in real time.
2. Comprehensive services
The SECaaS model allows you to acquire a comprehensive suite of security offerings at an affordable cost. And because you can combine SECaaS software from different vendors, you benefit from building a best-in-class security suite.
Perhaps you want Okta to handle your IDaaS needs while Bitdefender GravityZone Business Security protects your computing devices.
3. Cost savings
SECaaS is less costly than setting up in-house security. You buy the level of SECaaS protection required for your organization’s size, so you only pay for what you need.
The monthly subscription fees may seem like they add up to a big expenditure, but in-house security is far more costly. You avoid investing in the required security hardware, software, and personnel through a SECaaS solution.
IT security also requires continuous investment to keep pace with the latest cybersecurity technologies. The SECaaS provider shoulders these costs and responsibilities.
Even if your IT team is responsible for your company’s security, it still requires tools and insights that SECaaS solutions provide for a fraction of the cost required to develop these yourself.
4. Scalability
With a SECaaS vendor managing your security, you can focus staff and company resources on growing your business. As your business needs evolve and expand, the SECaaS provider can scale with your business.
Your SECaaS vendor can also deliver superior security since that’s its sole focus. It can stay on top of new security threats, monitor for vulnerabilities, and address potential issues in a timely manner before any harm befalls your organization.
Features of SECaaS
Many types of SECaaS solutions exist. Some vendors provide a complete range of services while others specialize in specific areas.
Here are some of the most common SECaaS capabilities offered today.
Network security
Any business with multiple computers connected to the same IT systems requires security for this network. This task becomes more complex when you’ve got remote workers.
SECaaS delivers network security best practices. Your network receives protection through tools, constant monitoring, and the implementation of IT policies, such as limiting access to websites deemed high risk.
Endpoint security
The laptops, mobile phones, servers, and other computing devices used by your business are collectively called endpoints. They’re often the targets of cyberattacks because they house many vulnerabilities a criminal can exploit.
This reality makes endpoint security software a must. Antivirus is the most common form of endpoint protection.
Robust SECaaS security extends beyond antivirus into services such as endpoint detection and response (EDR).
Email and web security
Email is one of the highest-risk areas in a business. Criminals often attempt to trick employees into clicking email links or attachments designed to look like an official note from a customer, bank, or other trusted source.
Once the employee does, this action activates a virus or other malware, infecting the employee’s computer. A computer connected to your IT network allows the infection to quickly spread to other endpoints.
Another risk area includes websites. Criminals can infect an unsecured website, causing any visitor to become infected with malware. Or criminals will create a fake website that looks like your bank to trick you into providing login information.
SECaaS software often includes email and website security components. The email protection blocks potentially dangerous emails and attachments. Its website security service does the same for dangerous sites.
Security assessments
A security assessment is one of the first actions a SECaaS solution performs. An audit of your organization's existing security measures is necessary to identify and address vulnerabilities, such as outdated software on your endpoints.
Ongoing security assessments are also required. Technology, and your business, evolve over time; continuous assessments ensure your systems are always protected.
Security information and event management
Security information and event management (SIEM) is the process of collecting disparate data from across an organization’s software applications, security devices, and IT network to analyze it for signs of a cyberattack.
Many types of malware exist, and some are so sophisticated they can avoid detection. SECaaS capabilities such as SIEM find these hidden threats before damage can occur to your organization.
Business continuity and disaster recovery
This area focuses on helping a business recover as fast as possible from a cyberattack or other incident causing disruption to its IT services.
If an attack takes down your website, you lose customers every second it's not available. A business continuity and disaster recovery effort aims to restore normal operations quickly. The goal is to achieve this outcome so fast, you don’t notice there was a problem.
Data loss prevention
Many cybercriminals are after your company’s data, particularly financial and customer records. Data loss prevention (DLP) protects your data through tools that monitor and verify data security.
Even if malware encryption such as Ryuk ransomware compromises your data, a DLP strategy ensures you’re still protected through proper backups and storage of your data.
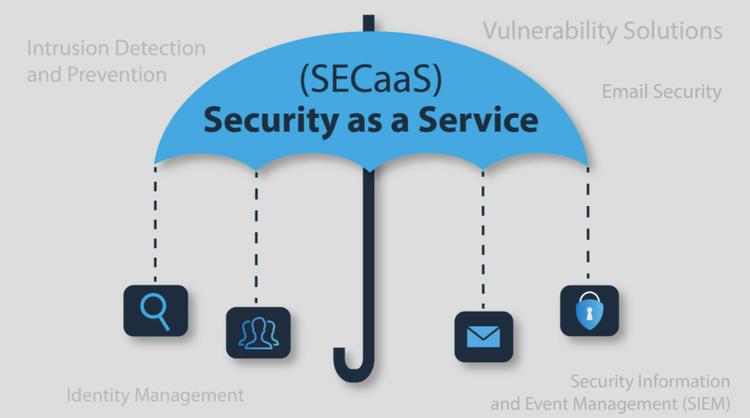
SECaaS is the umbrella uniting various security services. Image source: Author
How to choose SECaaS software
Selecting the right SECaaS solutions for your organization is the key to proper protection. To make this important decision, look for these capabilities.
1. Always available
The SECaaS security you purchase must operate at all times. SECaaS software should constantly monitor your IT systems for signs of attempted security breaches.
If you rely on a provider to perform monitoring or actions such as EDR, it should be able to deliver these even in the dead of night and on holidays. Cybercriminals don’t take time off, so your security can’t either.
2. Fast response
When a cyberattack happens, your security must respond immediately. This response takes several forms:
- The software sends an automatic alert notifying key stakeholders of a possible issue.
- The software takes action automatically to remediate any threat.
- The software interface immediately surfaces up key information about the attack, so security personnel can gauge the extent of the issue and how to prevent a similar attack in the future.
Look for SECaaS providers that can deliver a fast response in all of these different ways.
3. Data protection
A key capability of any SECaaS offering is protecting your company’s data. A ransomware attack that manages to encrypt critical files can cripple a business.
A good SECaaS solution provides data backup services so you have copies of your data stored in a safe location.
The software should also offer data encryption. If a cybercriminal gets to your data, it’s encrypted to prevent them from gaining access to its contents.
4. Security insights
If your IT team is responsible for company security, it requires the necessary information to make informed decisions. SECaaS software provides these insights.
The software also highlights areas of vulnerability. For instance, it identifies endpoints with outdated applications to update or remove.
5. Remediation and recovery
The reality is that no level of protection can stop all attacks. So, a SECaaS solution should equip your organization for this eventuality.
Look for SECaaS software that not only scans for an attack but can act against a threat. This includes blocking attacks from spreading across your IT network by automatically cutting off an infected machine.
A SECaaS solution should also prepare your organization to recover from a cyberattack. This includes helping you clean an infected endpoint so you can use that device again and automatically making copies of your data to use in restoring compromised files as quickly as possible.
6. Varied pricing
Varied pricing is a strength of SECaaS solutions. This allows you to pay only for the services you need. For instance, you pay for endpoint security software based on the number of endpoints you’re protecting.
Pricing should accommodate the ability to mix and match services and avoid locking you into a single vendor. For example, the cost of a SECaaS vendor’s security software used by your IT team is separate from the price of managed services provided by the vendor.
7. Ability to grow
Look for SECaaS solutions with the capacity to grow as your business needs evolve. If you’re trying to protect a dozen endpoints today, but may need to expand that number to hundreds or even thousands in the future, ensure the SECaaS offerings can accommodate this growth.
If you work in an industry with regulatory requirements, you’ll also want to ensure the SECaaS solution can accommodate your industry’s compliance needs as well.
Best practices when using SECaaS
The ability to control your IT environment is central to effective SECaaS implementation and security. Here are best practices to ensure the integrity and resiliency of your IT systems.
Frequent assessments
When you first implement a SECaaS solution, it’s natural to do an assessment to strengthen your organization’s security. But assessments must happen on a regular, ongoing basis.
An outdated app creates a security vulnerability. You may find employees visiting risky websites. Cybercriminals may discover a vulnerability before an app can release a fix.
A SECaaS solution can automatically perform these assessments and provide recommendations. It’s also plugged into threat intelligence to know about new threats quickly and evaluate if your IT systems are at risk.
Data policies
Data protection is a key component of SECaaS offerings. Part of this involves determining your data policies.
Do you need to perform data backups daily or more frequently? Where do you store copies? Who has access to this data? Is the data encrypted? What’s your data retention policy?
Figure out a data strategy with your SECaaS partner to ensure protection of your sensitive information and quick recovery from an attack.
Security policies
Part of setting up a SECaaS solution involves defining the security policies for the access and use of your organization’s IT assets and resources. It’s not something you set once and forget.
These policies must evolve over time. What you start with may require changes to strengthen existing policies, or you find some policies are hindering work productivity and necessitate adjustments. SECaaS software should allow flexibility in your security policies.
Identity and access management
Who can use your IT systems? What level of access to sensitive systems and data do they get? Address these identity and access management (IAM) considerations as part of your SECaaS platform.
IDaaS, a subset of IAM, solves the specific challenge of users needing access to disparate software and managing the various passwords for each. The best identity management software as part of a complete SECaaS solution helps resolve IAM needs.
Disaster recovery
A plan to address recovery from an attack or other IT disaster is a must. Sooner or later, you’ll run into an issue that causes a major outage to your IT systems.
SECaaS solutions should involve a disaster recovery component. These include data backups and storage and the ability to roll back software to a state before the disaster.
Reporting and alerts
Reporting is fundamental to any software platform and SECaaS is no exception. Some of the reports provided by SECaaS solutions include the ability to view your current security posture at a glance and an analysis of system vulnerabilities.
Alerting is also important to your security. You need to know of a potential attack in real time, and alerts provide that awareness.
Final advice about SECaaS
SECaaS is an evolving space. No single vendor is best in all IT security areas. Some excel at IDaaS, others at endpoint security.
To obtain a comprehensive SECaaS solution, you must identify your company’s IT security needs. Then add the appropriate security software to your SECaaS suite. In doing so, ensure your SECaaS choices support interoperability across different software.
The SECaaS model puts the onus on the small business to perform its due diligence, examining various SECaaS vendors to make your selections. But SECaaS also provides the greatest flexibility to tailor a security solution that makes sense for your business.
Our Small Business Expert
We're firm believers in the Golden Rule, which is why editorial opinions are ours alone and have not been previously reviewed, approved, or endorsed by included advertisers. The Ascent does not cover all offers on the market. Editorial content from The Ascent is separate from The Motley Fool editorial content and is created by a different analyst team.